Since March 2018, and with the release of Microsoft updates for Windows Server and Windows 7/10, Credential Security Support Provider protocol (CredSSP) has been triggered .

An authentication error has occurred.
The function requested is not supported
Remote computer:
This could be due to CredSSP encryption oracle remediation.
For more information, see https:/go.microsoft.com/fwlink/?linkid=866660
Root Cause Analysis
To resolve a vulnerability issue with Credential Security Support Provider protocol (CredSSP), a monthly Windows update in May was applied which does two things:
1. Correct how Credential Security Support Provider protocol (CredSSP) validates requests during the authentication process
2. Change the group policy Encryption Oracle Remediation default setting from Vulnerable to Mitigated.
This RDP authentication issue can occur if the local client and the remote host have differing Encryption Oracle Remediation settings that define how to build an RDP session with CredSSP. If the server or client have different expectations on the establishment of a secure RDP session the connection could be blocked. There is the possibility that the current default setting could change from the tentative update and therefore impact the expected secure session requirement.
Resolution/ Fix
Ensure both client & server side have latest patch installed so that RDP can be established in a secure way.
Alternative Work-arounds
Resolution 1
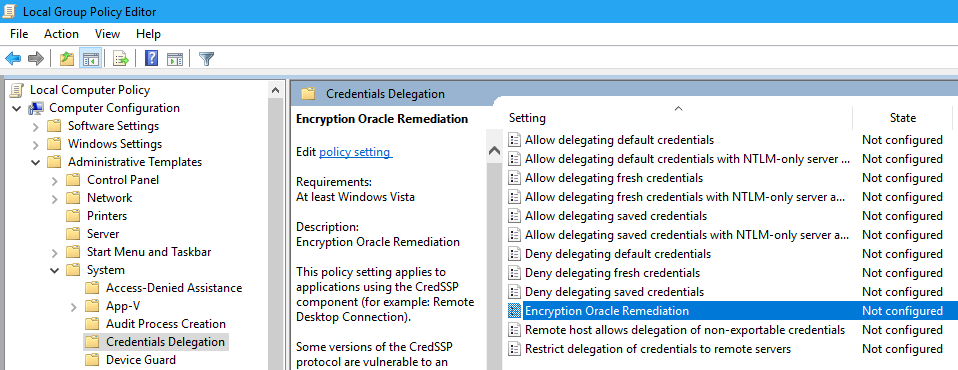
If you cannot RDP to VMs from your patched client, we can consider changing the policy settings on the client to temporarily gain RDP access to the servers. You can change the settings in Local Group Policy Editor. Execute gpedit.msc and browse to Computer Configuration / Administrative Templates / System / Credentials Delegation in the left pane:
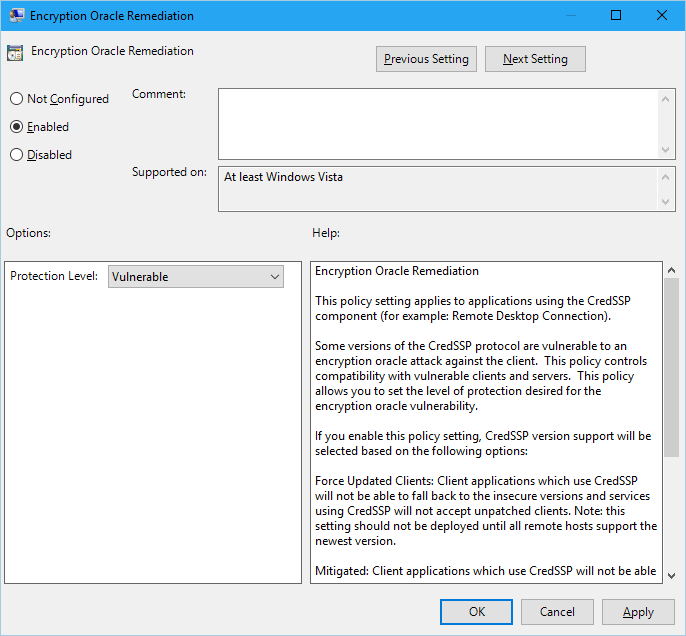
Change the Encryption Oracle Remediation policy to Enabled, and Protection Level to Vulnerable
Same steps on Windows 7 / 10
Resolution 2
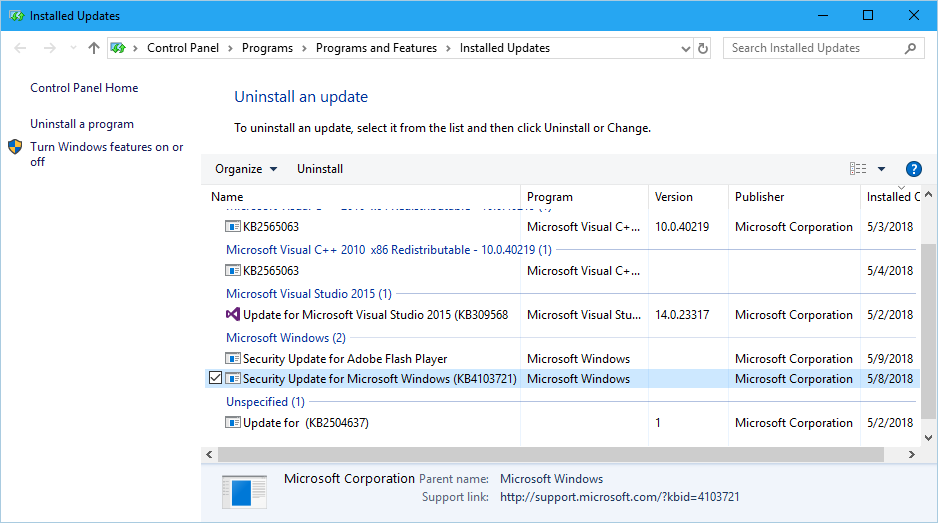
If your Windows client does not have group policy editor gpedit.msc or above “Oracle Remediation” option:
Windows 10
Windows 7
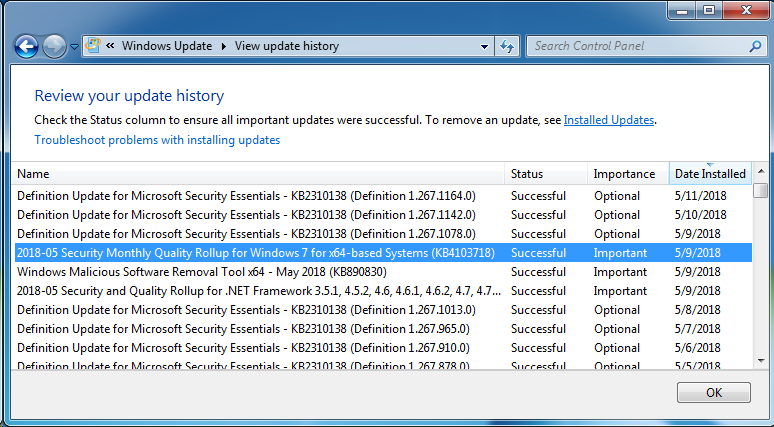
Remember to reinstall it when you are done.
Resolution 2 Work Around
If it is not possible to access to Local Group Policy Editor on the client (i.e. Windows Home versions), same change can be done through the registry:
HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\System\CredSSP\Parameters\ /v AllowEncryptionOracle /t REG_DWORD /d 2
After that, whether the established RDP session is secure or not depends on whether server is patched. Remember to undo this when all the servers are patched.